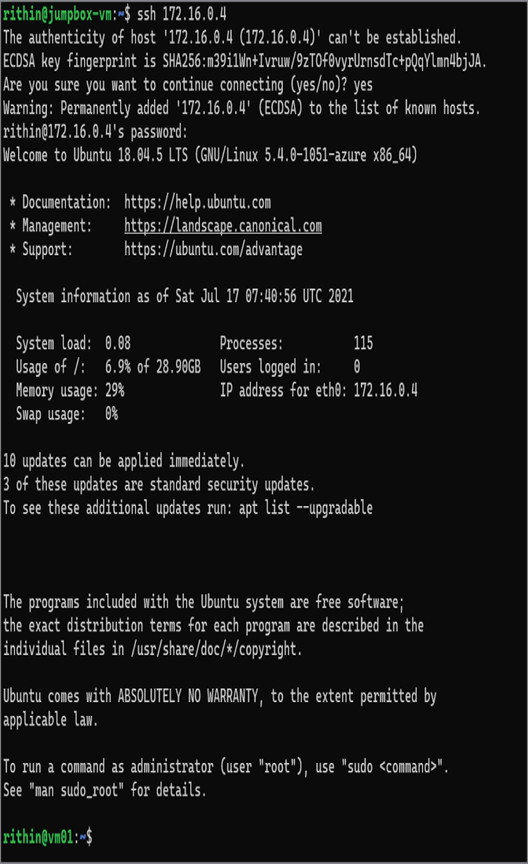
5. You will be asked the save the host signature and then enter the password. Once authenticated, you will be able to see that you are connected to vm-01. The following image is from Windows Terminal; depending on what SSH client you are using, the color schemes may vary.
- Now, you need to find the private IP address of vm-02. You can follow the steps you performed for vm-01 to find the private IP of vm-02. If you used the PowerShell script, probably the private IP address would 192.168.0.4.
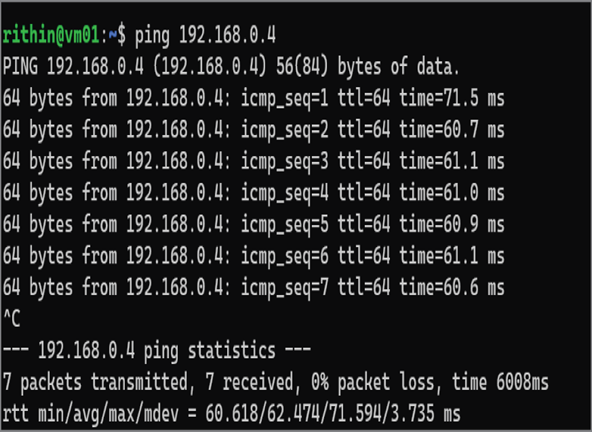
- From the terminal, try ping 192.168.0.4 and note the response. It’s expected that you don’t get any response as vnet-01 and vnet-02 is not configured to communicate with each other. You can exit out of ping by hitting Ctrl+C on your keyboard.
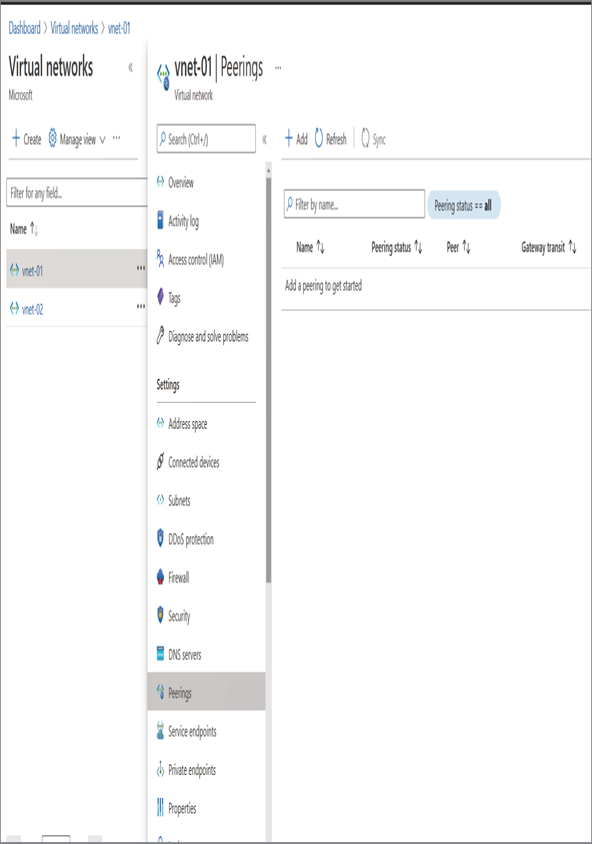
- You will configure the peering now so that vm-01 can communicate with vm-02. For setting up the peering, navigate to the Azure portal and search for virtual networks. Click Virtual Networks, which will take you to the list of virtual networks in your subscription.
- As mentioned in the introduction of this section, you can set up a connection from any one of the networks that you want to peer, and the reciprocal connection will be created on the other network.
- Click vnet-01 and jump to the Peerings blade. Then click + Add to start the peering creation process.
11. Provide the information as follows:
- Peering link name: This is a friendly name given to the link that you are creating in vnet-01. It’s always recommended that you give names that you can use to understand the peering. For example, here you are connecting to vnet-01 to vnet-02. To recognize this connection, you can name it vnet-01-TO-vnet-02. This will help you recognize the connection in the future.
- Traffic to remote virtual network: This is for you to control whether you want to allow traffic from vnet-01 to vnet-02. In your case, you will set it to the default value, which is allow.
- Traffic forwarded from remote virtual network: This is for you to control what action needs to be taken on any traffic coming to vnet-01, which is forwarded by vnet-02. It is mentioned as forwarded because the origin of the traffic is not vnet-02. You will go with the default value allow.
- Virtual network gateway or route server: This option is used when you are dealing with dynamic routes. In your case, you will go with none, which is the default value.
- Peering link name (remote virtual network): You need to provide a name for the reciprocal connection, which will be created on vnet-02. For simplicity, let’s call it vnet-02-TO-vnet-01.
- Virtual network deployment model: To select the classic or ARM network, you will select the Resource manager as we created vnet-02 as an ARM resource.
- I know my resource ID: If you know the resource ID of the remote network, then you can check this box and provide the resource ID. Let’s keep it unchecked and select your vnet-02 by selecting the subscription.
- Subscription: You can select the subscription where your remote network (vnet-02) resides. This option will not be shown if you are going with the resource ID option.
- Virtual network: Once the subscription is selected, Azure will list all virtual networks in the subscription. Select the desired subscription from the drop-down. In your case, you will go with vnet-02.
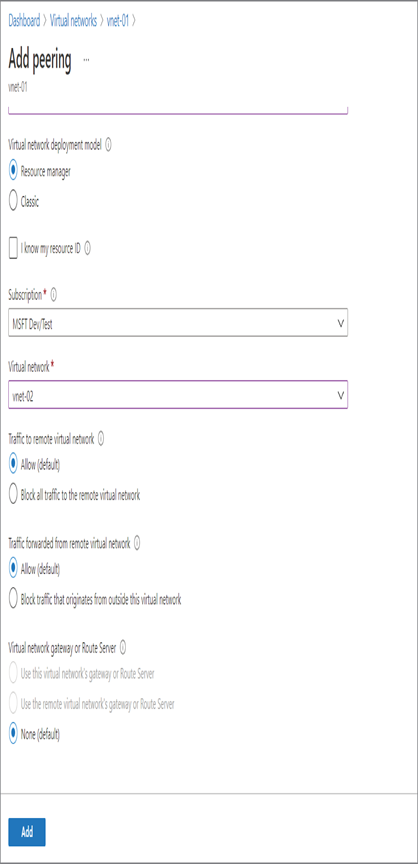
- Additionally, you will be asked to fill the traffic to the remote virtual network and forwarded traffic configuration. Set these values to the defaults. These are the properties of the peering link that will be created in vnet-02. In other words, here remote refers to vnet-01.
- Once you provide the information, click OK to create the peering. You can see that two connections are getting created.
- After 7 to 10 seconds, if you navigate back to the Peering blade, you can see the peering and the peering status as Connected. If you navigate to vnet-02 ➢ Peering, you will see the reciprocal connection also with the connected status.
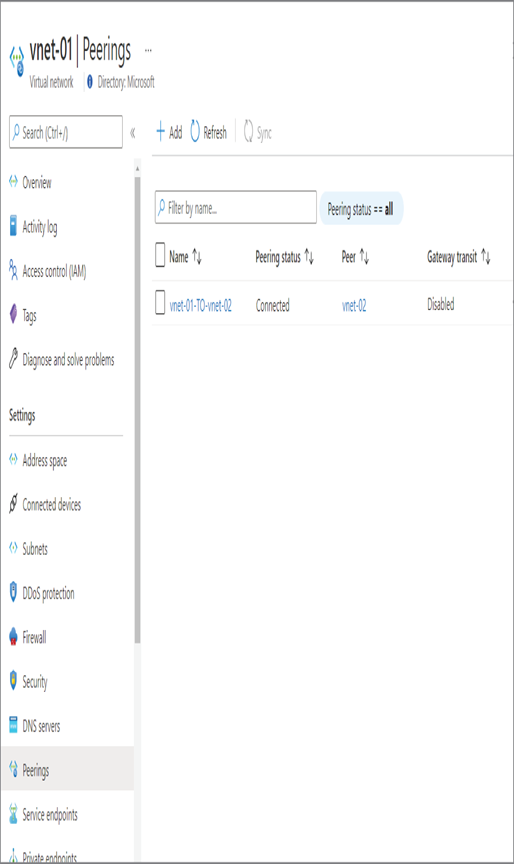
14. It’s time to verify the peering. Switch back to the SSH terminal (or reconnect to vm-01 if you closed the connection) and try pinging the private IP address of vm-02 from vm-01. Unlike the last time, you will see that you are getting a ping response from the vm-02.
With the implementation of virtual network peering, the VM deployed in vnet-01 is able to communicate with VM deployed in vnet-02. The landscape and architecture of your network will change when there is a business requirement, so it’s essential to know how you can modify the existing peering to accommodate the network changes.
Leave a Reply