When you create a VPN gateway, you will be asked to choose how to configure HA in the VPN gateways. There are two options by which you can implement HA in VPN gateways: active-standby and active-active. Now, you will see the HA configuration these models.
Active-Standby In Azure, each VPN gateway is configured in an active-standby configuration with the combination of two instances. During an event of any planned maintenance or unplanned interruptions to the active instance, Azure will automatically fail over to a standby instance. Once the failover is completed, the standby will resume all S2S and virtual network-to-virtual network connections. The IP address of the VPN gateway will remain the same. There will be a small interruption during the failover process. It takes about 1 minute, and in a worst-case scenario, it can go up to minutes. The P2S connections’ gateway will be disconnected during the failover process; clients will need to reconnect to the VPN as there will be a connection drop. Figure 4.8 shows how the active-standby configuration is set up for a virtual network-to-virtual network and on-premises gateway.
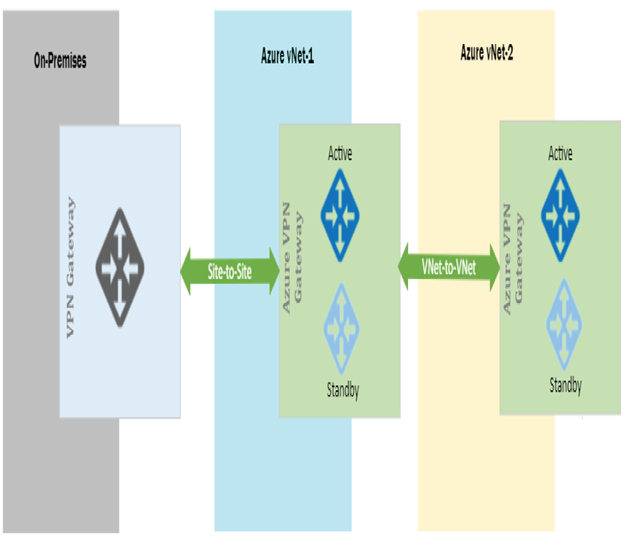
FIGURE 4.8 Active-standby configuration
In Figure 4.8, you can see that a virtual network to virtual network connection is established using an active-standby configuration. You can set up on-premises high availability based on your requirements, and it’s up to on-premises administrators to set that up. Active-standby is the default configuration whenever you create a VPN gateway; this can be changed to active-active by changing Enable Active-Active Mode to Enabled.
Active-Active You can also configure active-active configuration in your VPN gateway, and in this configuration S2S connections will be established from both instances to your on-premises VPN device. In the case of a virtual network to virtual network connection and S2S connection, the tunnels will be established as shown in Figure 4.9.
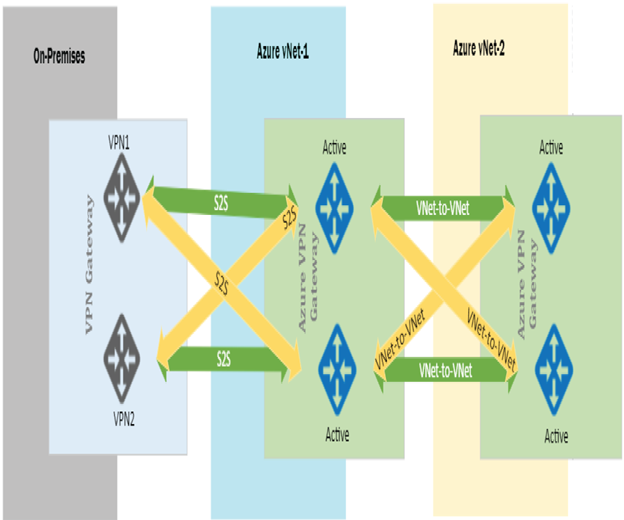
FIGURE 4.9 Active-active configuration
Here each instance will have its own public IP address on both sides of the virtual network. You need to let each instance know about the other two peers for establishing two tunnels. In the case of on-premises, you need to set up both of your VPN devices with the public IP addresses of the gateway instances.
In an active-active configuration, the traffic is routed concurrently through both tunnels. If a maintenance event or unplanned event occurs to one of the instances, the tunnel from that instance is terminated, and the communication will happen only through the other instance. This failover is automatic, and no intervention is required from your end.
I hope this gives you an understanding about the gateway high availability configuration. With that you will start setting up your virtual network-to-virtual network connectivity using VPN gateways.
Leave a Reply