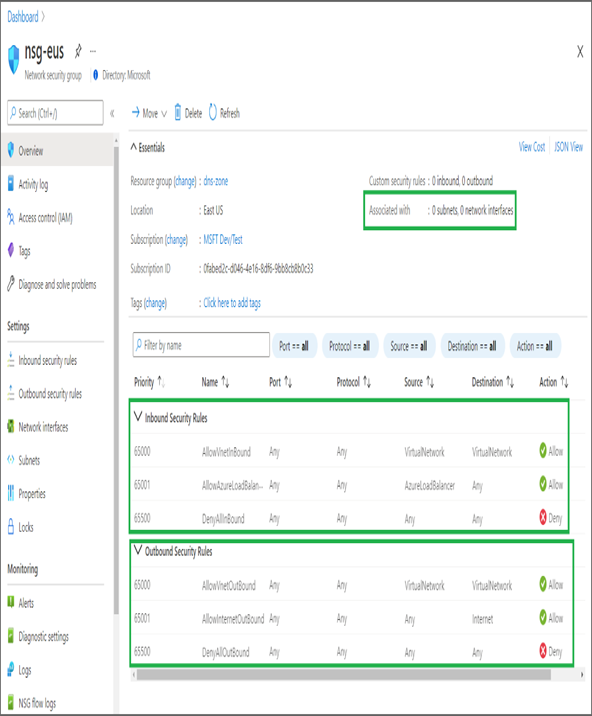
Once you create an NSG, from the Overview blade, you will be able to see the associations made to the NSG. Associations include subnet, NIC, and security rules. After creating the NSG, you will add rules that will be associated with the NSG. See Exercise 3.10.
EXERCISE 3.10
Creating NSG and NSG Rules
- Sign in to the Azure portal and search for Network Security Groups. Once you are in Network Security Groups, click Create.
- To create an NSG, you need the subscription name, resource group, name of the NSG, and region.
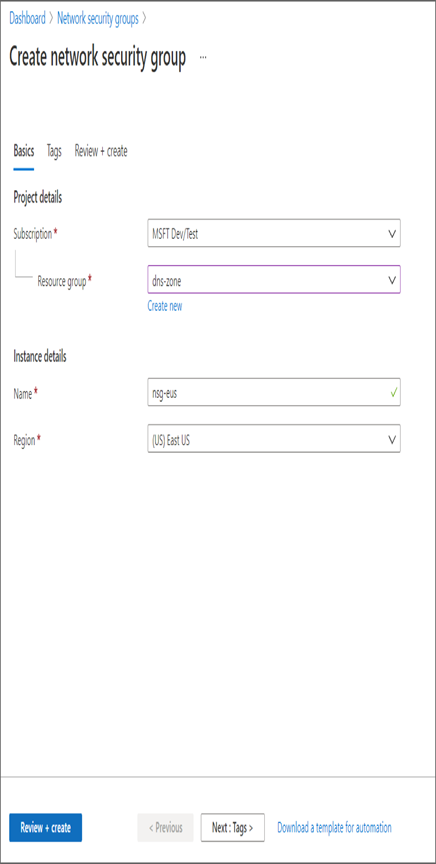
- Once you have filled in the parameters, click Review + Create to start the validation. After validation, click Create to create the NSG.
- After creating the NSG, navigate to the NSG you created. The Overview blade will show the associations and the rules (both inbound and outbound).
5. Click Inbound Security Rules and then Add to add a rule. As shown, you can add a rule by specifying the source, destination, port, protocol, action, priority, and name of the rule.
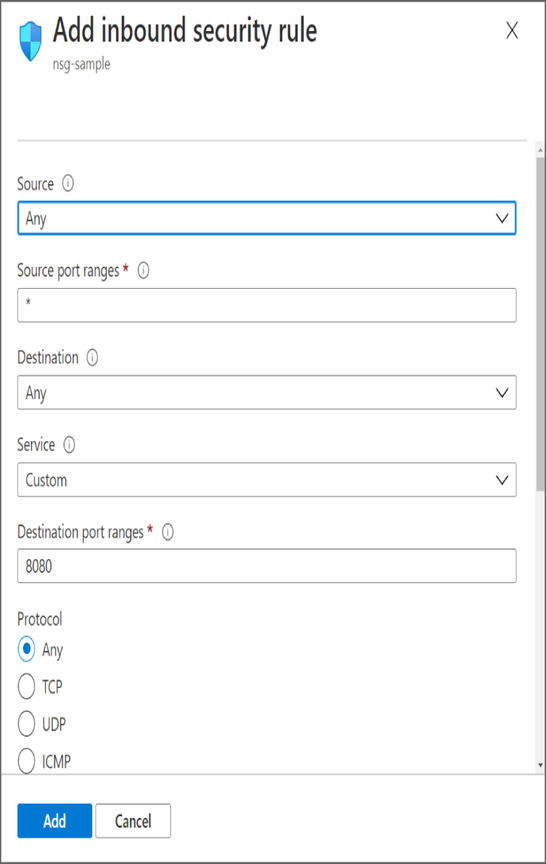
- Similarly, you can create outbound security rules by navigating to the Outbound Security Rules blade.
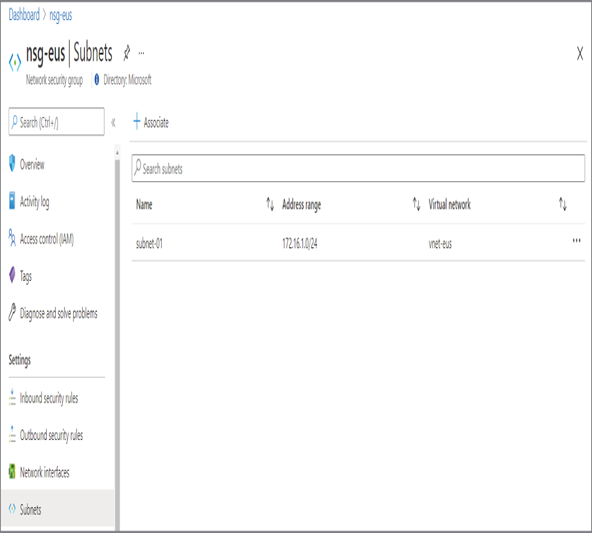
- Once the NSG rules are created, you can navigate to the Subnet or Network Interfaces blade to your associated NSG.
Now that you know how to create an NSG, add rules, and associate the NSG with subnets or NICs, you will look at the concept of effective rules.
NSG Effective Rules
If you are using NSGs at both the subnet and NIC level, the rules will be evaluated at both levels. For the traffic to be allowed, there should be an allow rule created at both the subnet and NIC levels. If any level doesn’t have an allow rule, the traffic will be dropped. When you assign an NSG to a subnet, the rules will get applied to all NICs that are part of the subnet. You can override this inheritance and have a dedicated rule assigned to a NIC. When you apply NSG to both subnet and NIC, then effective rules come into the picture.
As mentioned earlier, each security rule will be evaluated independently when the NSG is applied to both the subnet and NIC levels. Incoming traffic will be first evaluated against the rules applied on the subnet level; if there is an allow rule, then the packet will be sent to the NIC. The rules set at the NIC level will be evaluated now, and only if there is an allow rule then the packet is allowed; otherwise, it will be dropped. Similarly, all outgoing traffic will be first evaluated against the NIC rules; if there is an allow rule, then the traffic is evaluated at the subnet level.
Having the ability to apply a rules subnet and NIC level reduces administrative overhead; rules at the subnet level can be always overridden by applying another set of rules at the NIC level.
Leave a Reply